This is part 1 of a new three-part article about Continuous Integration Strategies. We hope you enjoy it!
EXECUTIVE SUMMARY
Continuous Integration (CI) offers a method of avoiding the integration issues that typically occur when there are extended periods between developers checking in working copies of code. However, the technique also offers significant benefits where an application is designed to run on multiple versions of a platform and the application and platform are changing. In both cases, Continuous Integration facilitates the early detection and eradication of software defects: defects that may otherwise go undetected for days, weeks, or months after they were created. Detecting and resolving these problems early in the development process can translate into lower costs and shorter timelines.
This paper aims to simplify the adoption of Continuous Integration by software vendors targeting Red Hat® Enterprise Linux®. It does this by providing guidance on:
- Accommodating changes in application software and the OS.
- Versions of Red Hat Enterprise Linux against which an application should be tested.
- Test creation.
- Setup and maintenance of the test environment.
Overall the reader will gain an understanding of what should be considered to give the widest possible assurance that the product will run on Red Hat Enterprise Linux.
By adopting the practice of Continuous Integration and the recommendations in this white paper, application developers targeting Red Hat Enterprise Linux will be able to offer their customers a higher degree of assurance that software will perform as expected. An additional benefit is that achieving self-certification should be easier, providing further reassurance to customers.
THE PROMISE OF CONTINUOUS INTEGRATION
The time between the introduction of a software defect and its detection can have a dramatic effect on the elimination of that defect: find the defect soon after its introduction, with the relevant changes fresh in the developer’s mind, and it will be easy to eliminate — find it later, after the details of the change have faded, and the solution can be elusive.
At the same time, any project that has multiple developers working on multiple code streams will face the inevitable requirement to integrate these code streams back into the mainline—and once again, the longer each working copy has been separated from the mainline and the greater the number of working copies, the more likely that integrating code changes to the mainline will be a challenge and the effort required difficult to predict.
There are two additional issues that can complicate development if integration and testing aren’t performed regularly.
Where issues are identified with a target platform, it’s not uncommon for the application developer to code workarounds into the application software, increasing code complexity and reducing maintainability. There may be no need for a workaround, however, if a patch for the target environment already exists. Checking for platform updates as a part of the integration and testing process enables timely patch validation against applications, eliminating the need for workarounds in many cases.
There are also a small but functionally significant number of libraries where innovation and improvement mean that changes occur regularly, such as Mozilla XULRunner. Again, here regular testing as the library and application change will reduce the likelihood of the ‘surprises’ inherent when there are protracted periods between build and test cycles.
Continuous Integration (CI) is a technique that seeks to minimize these issues by integrating soft- ware changes into the mainline code continuously—usually several times a day—then building and testing the software to identify any defects that can then be quickly rectified, maintaining the integrity of the software.
For Red Hat Enterprise Linux software vendors, the CI environment needed may seem complex because developers need to build and test against multiple production environments that reflect environments operated by various customers or impending new releases.
This whitepaper looks at CI in general, but focuses on the particular requirements that the real world diversity of Red Hat Enterprise Linux installations imposes on software vendors—offering guidance on creating a testing regime and test environments to optimize the testing strategy.
CI BASICS
Continuous Integration emerged as part of the Extreme Programming development process in the late 1990s, where it is one of the original twelve practices. As a result there is already a significant body of knowledge regarding CI (see the references section). Therefore this paper provides only a summary overview of the components needed for CI implementation and the process involved in operating such an implementation.
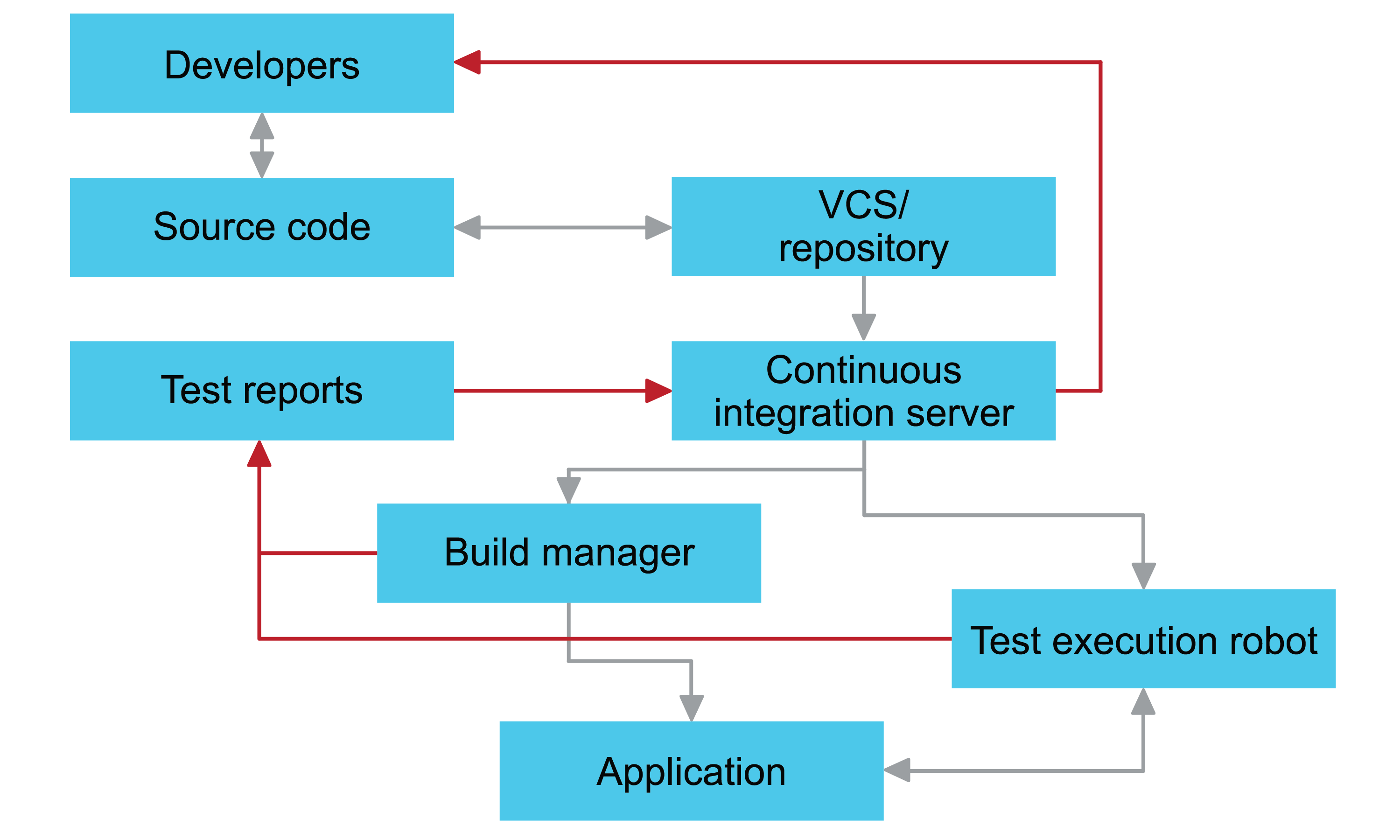
A typical Continuous Integration environment might contain the following key components:
- A developer modifies source code and any related artifacts required to implement defined changes, and then pushes the changes into a version control system/repository (for example Git or Subversion).
- A continuous integration server, such as Jenkins, Travis, or Wercker, monitors changes in the repository and identifies the need for an integration build/test and runs:
- The build manager—such as Apache Ant, Apache Ivy, Gradle, or Apache Maven—to create the application (providing test reports as it does so).
- An environment provisioning tool—such as Red Hat Satellite, Cobbler, Ansible, Puppet, Chef, or BoxGrinder—to create the environments in which to test the software against one or more ver- sions of an operating system.
- A test robot—such as Beaker, or Autotest for native applications or Selenium for web apps—to execute integration and end-to-end tests on the build application, again providing test reports as it does so.
- The continuous integration server parses the test reports and provides feedback to the developer. At this point, the developer either implements any necessary defect fixes or continues with the application development.
 View part 2 here.
View part 2 here.
