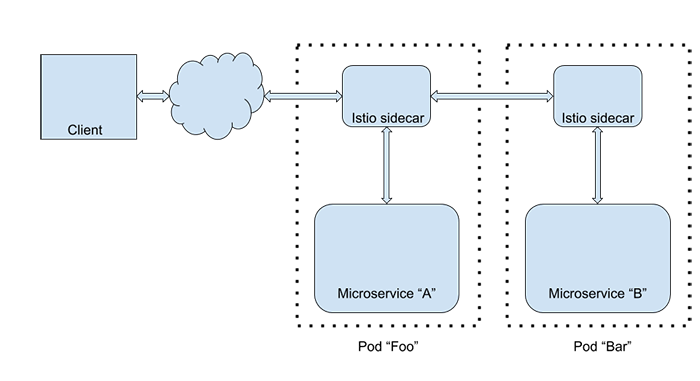
Istio: Canaries and Kubernetes
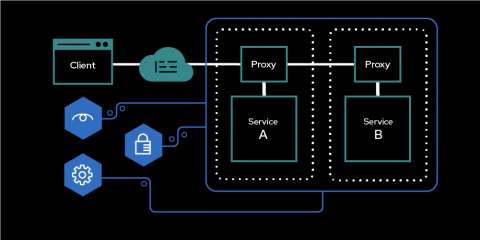
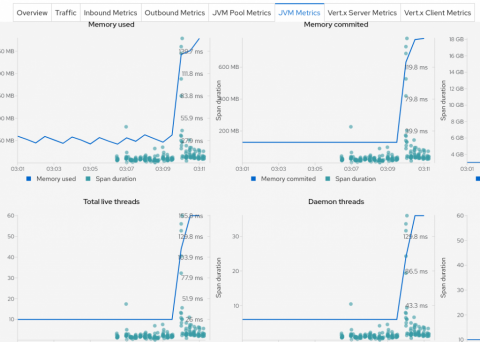
In this session, we will introduce you to cloud native architecture by demonstrating numerous principles and techniques for building and deploying Java microservices via Spring Boot, Wildfly Swarm and Vert.x, while leveraging Istio on Kubernetes with OpenShift.