What is Secure Coding?
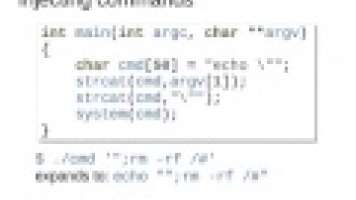
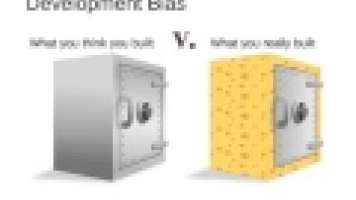
Secure coding is a set of technologies and best practices for making software as secure and stable as possible. It encompasses everything from encryption, certificates, and federated identity to recommendations for moving sensitive data, accessing a file system, and managing memory. Although the security landscape is always changing, secure coding tries to make building secure software more of a science than an art.