Cryostat is a container-native JVM application that provides a secure API for profiling and monitoring containers with JDK Flight Recorder (JFR). Cryostat introduces the concept of Match Expression in Automated Rules and Stored Credentials that it uses to check whether the rule or credential should apply to a target JVM. To learn more about Match Expression, check out Automating JDK Flight Recorder in containers.
With Cryostat 2.3, Topology View is introduced to provide a visual presentation of the all discovered JVMs and all resources that are associated with them. A subset of its features are used to bring about the brand new Match Expression Visualizer that allows you to see which targets are matched as you type in the Match Expression.
To learn more about Topology View, check out Getting Started with Topology View in Cryostat 2.3.
Prerequisites and Setup
To get started, you need to install Cryostat 2.3. With Red Hat OpenShift Platform, you can install Cryostat using Cryostat Operator. For more details, Installing Cryostat.
Visualizer with Automated Rules
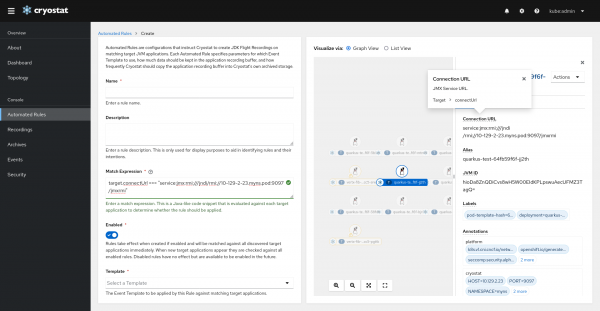
Navigate to the Automated Rules page and click Create to open the Automated Rules form.
To see target details, click on the target node of interest. This will open a drawer panel with the target information. Click on the field name to see its explanation and field path used in Match Expression. For example, Target > connectUrl means we can use target.connectUrl === connectionUrl.
Enter the Match Expression field. The graph view will highlight which targets are matched. Unmatched targets will fade.
The Match Expression Visualizer also supported List View mode, where matched targets are shown as rows. Expand the row to see the target detail.
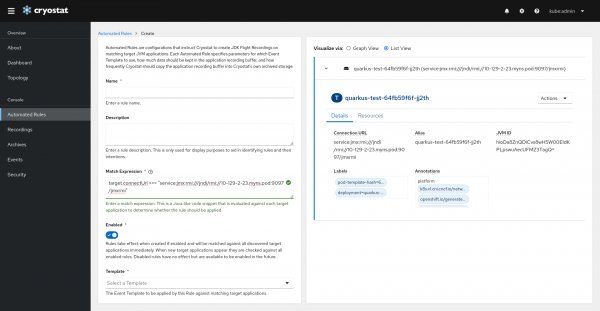
Figure 2. Using Match Expression Visualizer (List View) with Automated Rules form.
Visualizer with Store Credentials
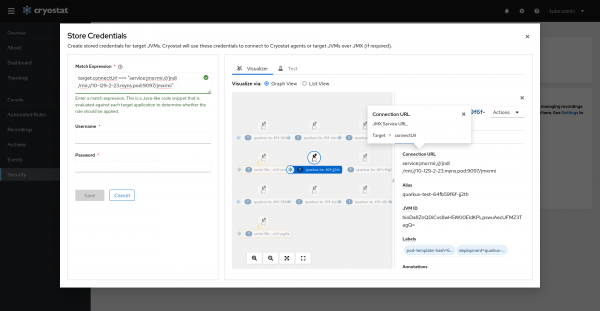
Navigate to the Security page and click Add to open the Stored Credentials form.
Enter the Match Expression field. Notice the same visualizing features are supported here as in Automated Rule form.
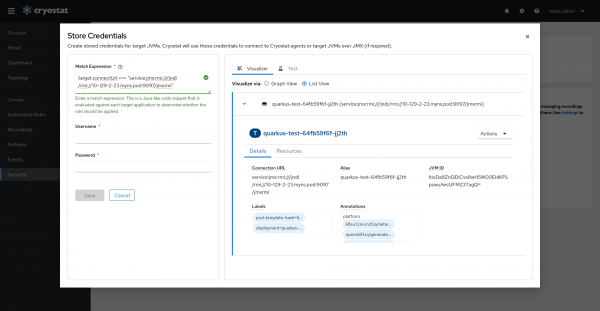
You can also switch to List View. Expand the row to see the target details.
Conclusion
Cryostat uses Match Expression in Automated Rules and Stored Credentials to check whether the rule or credential should apply to a target JVM. In Cryostat 2.3, Match Expression Visualizer allows developer to see which targets being matched as they type in the Match Expression.
