
Use compiler flags for stack protection in GCC and Clang
Smash-stacking attacks are common, but the GCC and Clang compilers have a number of flags that can help defend against them. Read on for more info.

Smash-stacking attacks are common, but the GCC and Clang compilers have a number of flags that can help defend against them. Read on for more info.

You can compile Go code on Red Hat Enterprise Linux in such a way that it complies with U.S. Federal encryption standards. Find out how.
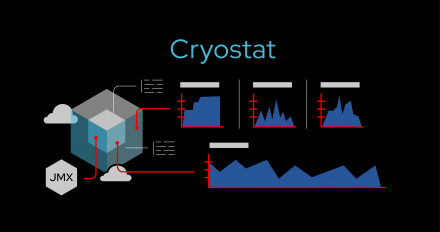
It is now easier to use Cryostat for monitoring Java applications on OpenShift. This article details changes to the login flow in Cryostat 2.1.

Use Red Hat's SSO with OpenLDAP to authorize producers and consumers for Kafka in Red Hat AMQ Streams

Red Hat's single sign-on technology can offer federated authentication through open source Kerberos. This article shows the steps to implementation.
A trip through Red Hat Developer's content for the month, with articles on GCC 12, Java in containers, Red Hat's SSO technology, and much more.

Learn how to configure a Quarkus Java application to authenticate with Red Hat's SSO on Red Hat Openshift or Red Hat Enterprise Linux.

Learn how to use Ansible to automate the installation and setup of Red Hat's single sign-on technology, which is based on Keycloak.
A practical guide through the jungle of modern development with Kubernetes, with a focus on application distribution via continuous integration/continuous delivery (CI/CD) and GitOps on Red Hat OpenShift.

Get started with new features in Red Hat Data Grid 8.3, including cross-site replication improvements, two new SQL cache stores, and Helm chart support.

Discover how Project Thoth solves dependency management issues and vulnerabilities in the Python ecosystem, making the resolution process cloud-based.

Improve your Kubernetes apps' security with runtime checks on sensitive activities. Record seccomp profiles using the Security Profiles Operator and eBPF.
Get step-by-step instructions to install and configure a self-signed certificate for secure HTTPS communication with Red Hat Decision Manager.

Extend common DevOps tools and processes with DevSecOps to improve app security. Enable security automation and help teams collaborate on security policies.

Get started with using Red Hat Universal Base Images for lightweight, secure, and free container builds, with examples based on Golang and Python.

Learn to automate dependency analytics by integrating code scanning into your CI pipeline. Use the CodeReady Dependency Analytics GitHub Action to spot flaws.
The latest, stable updates of development technologies for Red Hat Enterprise Linux.

Improve security by using biometric data for user authentication. Configure Red Hat SSO to use WebAuthn and deploy test client for biometric authentication.

An intelligent, distributed caching solution that boosts application performance, provides greater deployment flexibility, and minimizes the overhead of standing up new applications.

Set up the NVIDIA Morpheus AI application framework and NVIDIA BlueField-2 data processing units with Red Hat OpenShift and Red Hat Enterprise Linux.
Checkpoint/restore is useful when migrating containers in Kubernetes. Learn how this feature was implemented and how it's used in container migrations.

Learn how to connect to Red Hat Data Grid without using SSL. This service uses single sign-on tech (SSO) without SSL when you don't require secure connectivity.

Learn how Project Thoth's new security recommender makes a recommendation, then use the Thamos CLI to find security issues in your Python library code.
Learn to write, configure, and install a webhook that intercepts and validates Kubernetes requests, stopping users from creating rules with invalid fields.
Learn how to connect to external PostgreSQL databases via SSL/TLS for Red Hat's single sign-on technology (SSO). This technique ensures secure connectivity.