Get started with Red Hat Trusted Artifact Signer
Enables cryptographic signing, verification of software, and provenance metadata.
Learning resources

Learn how to install the Red Hat Trusted Artifact Signer using Google...
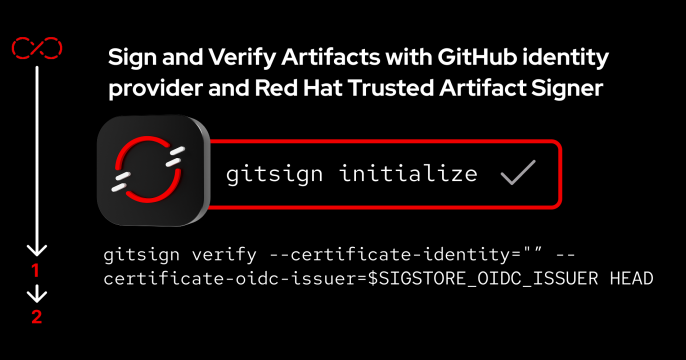
In this learning exercise, we'll set up the ability to sign and verify...

In this learning exercise, we'll learn how to automate the signing and...

In this learning exercise, you will learn how to secure your Jenkins pipeline...
Latest articles

Learn how Red Hat AI can help address the security challenges of AI agents in...

Learn about some of the quirks of running a build command in a distroless image.

Scale agentic AI with Red Hat’s trusted software factory. Use Policy as...

Deploy confidential containers and CVMs for AI. Learn how the Red Hat build...





