
Red Hat build of Cryostat 4.2: Enhanced Java monitoring for OpenShift
Explore new features in Red Hat build of Cryostat 4.2, including SQL query support for JFR analytics, async-profiler integration, and remote management for smart triggers.

Explore new features in Red Hat build of Cryostat 4.2, including SQL query support for JFR analytics, async-profiler integration, and remote management for smart triggers.

Use the Red Hat build of Podman Desktop to create a minimal, bootable Java
Learn to modernize enterprise Java for Kubernetes using the four-path framework. Explore cloud-native patterns like Sidecars, Sagas, and RAG to build resilient, AI-ready systems.

Learn how to install the Red Hat Data Grid operator in a disconnected OpenShift environment, with step-by-step instructions and details on the core components and architecture. This article also covers how the Data Grid operator manages operands and how Operator Lifecycle Manager installs operators.
Explore an automated, event-driven solution using streams for Apache Kafka, Debezium CDC, and Quarkus with SmallRye Reactive Messaging to sync failure analysis.

Headed to Devoxx UK 2026? Visit the Red Hat Developer booth on-site to speak to our expert technologists.

Headed to Devoxx France 2026? Visit the Red Hat Developer booth on-site to speak to our expert technologists.

Red Hat Customer Portal now offers Temurin JDK 25 for 64-bit Windows, providing another supported, production-ready option for running Java on Windows.
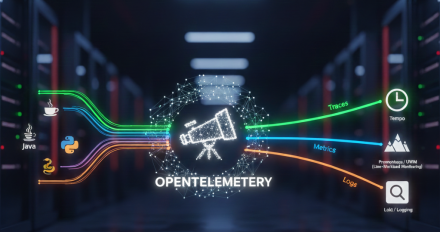
Learn about the Red Hat build of OpenTelemetry and its auto-instrumentation capabilities to achieve full-stack observability on OpenShift.
Headed to DevNexus? Visit the Red Hat Developer booth on-site to speak to our expert technologists.

The Red Hat build of OpenJDK is an open source implementation of the Java Platform, Standard Edition (Java SE).

Learn more about the Software Catalog and Templates in the Red Hat Developer Hub.
Headed to DeveloperWeek? Visit the Red Hat Developer booth on-site to speak to our expert technologists.

This article explores how to use the new features of Red Hat build of Cryostat 4.1 to diagnose problems on Java applications running in OpenShift or Kubernetes.

Discover the advantages of using Java for AI development in regulated industries. Learn about architectural stability, performance, runtime guarantees, and more.
Learn about the JBoss Web Server (JWS) container image and its deployment on Red Hat OpenShift 4. Explore default container settings and customization options.
Upgrade to Red Hat Enterprise Linux 10.1 and discover the benefits of OpenJDK 25 LTS, including better performance, memory efficiency, and developer ergonomics.
This in-depth guide helps you integrate generative AI, LLMs, and machine learning into your existing Java enterprise ecosystem. Download the e-book at no cost.

Your Red Hat Developer membership unlocks access to product trials, learning resources, events, tools, and a community you can trust to help you stay ahead in AI and emerging tech.

Red Hat build of Quarkus 3.27 offers enhanced data handling, observability, and
Learn about the Apache Kafka's KRaft protocol, a consensus algorithm that ensures fault tolerance and consistency in a network of interconnected nodes.

Explore new features in the JBoss EAP 8.1 release, including bootable JARs, self

Discover how Camel JBang's infra command simplifies local development by launching real back ends like Kafka and Artemis, eliminating complex mock setups.

The video demonstrates Camel JBang's infra command, showcasing how it simplifies prototyping by instantly launching backend systems like messaging brokers using Testcontainers and Docker. In this 15-minute demo, viewers will see a practical example of setting up and testing integration flows locally with minimal setup.
Headed to Devoxx Belgium? Visit the Red Hat Developer booth on-site to speak to our expert technologists.