So here's are deal: We've created what we're calling "PaaS-Containers" in our IT production environment. It consists of core technologies like RHEL Atomic Host, Kubernetes, and Docker along with supporting CI/CD components like Jenkins together as part of an offering that supports the end-to-end automated deployments of applications from a code-commit event through automated testing and roll-out through multiple environments (dev, QA, stage, prod). Oh, did I mention that it's also integrated with our enterprise logging and monitoring as well as our change management process and tooling so that we have a complete audit trail?
Everyone wants to jump on the bandwagon - they see the benefits of rapid deployment, atomicity, enabling business capabilities faster through technology. But as we learned in the 90-day initiative to get it stood up and an existing application deployed on it, all applications aren't ready for containers and some may never be based on their current architecture.
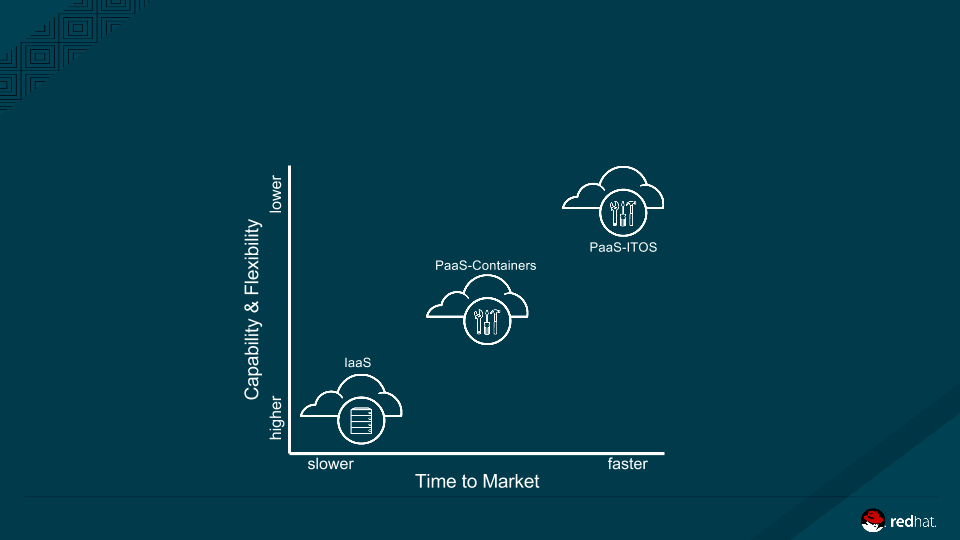
Here's what we think about the deployment options in an enterprise context that allows us to enable innovation while managing enterprise risk...
IaaS, PaaS, Containers, OpenShift Enterprise. I'm confused. What should I use?
In our environment, we offer a number of choices for development teams to deploy applications in addition to traditional virtualization (aka pets). We have IaaS and two flavors of PaaS: one we call PaaS-Containers (running RHEL Atomic, Kubernetes, and Docker with supporting CI/CD components across multiple environments to support our various security contexts); and one built on OpenShift Enterprise (OSE) 2.x that will be upgraded to OSE 3 in the near future (we call this IT OpenShift). This multifaceted approach allows our application teams to innovate rapidly while having full transparency from an enterprise risk and governance perspective.
So the question that application teams have is: which should I use?
An easy way to think about what you get with each of these offerings is the intersection of time-to-market against capability and flexibility. IaaS is the most flexible, but takes a bit longer to setup, configure and deploy. PaaS, on the other hand, imposes a number of constraints (like technologies, security contexts, or environmental support), but allows you to move very quickly.
So... Can I use the PaaS-Containers in the IT Environment for my App?
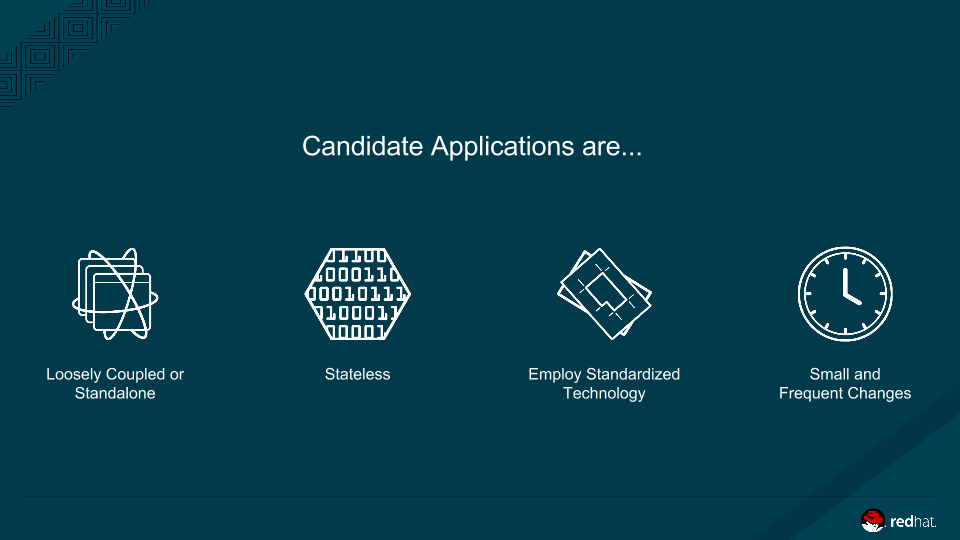
If an application team does think PaaS Containers offers the right balance to support the business needs, here are four aspects that we ask potential early-adopter application developers to think about to ensure we can support them in our enterprise context.
- Loosely Coupled or Standalone - the fewer interdependencies you have with other applications or between portions of your application, the easier off you'll be in this environment. Because of the automation and speed, coordination between several teams for concurrent releases becomes impractical. If you are typically coordinating with many other teams to synchronize releases during outage windows, this probably isn't the environment for you right now.
- Stateless - with PaaS Containers you will never know which hosts are running your application or even where they are, for that matter. While services can talk to each other within the environment, relying on state mechanisms that assume that the state will be available between requests should be carefully considered.
- Employ Standardized Technology - even though you can take a base image of RHEL and layer almost anything on top of it, in the IT environment for PaaS Containers, we have limited the technology stack to what we call Platform Operations "Blessed" images. These are secure images that lay down the necessary enterprise hooks and configuration to ensure a maintainable and secure environment for our applications that can be supported our Platform Operations team. Think of this as ensuring a secure supply chain for images.
- Small and Frequent Changes - if you're making large, complex changes to your application every couple of months, this is probably not where you'll want to be. Pushing small changes on a more frequent basis (daily) allows for stability in the business services the application supports. Your application should be able to have the changes tested and validated quickly to make this happen.
I'm sad - you can't support my application in the container environment. Now what?
In most cases, starting to make the necessary architectural changes to your application now, will enable you to move quickly - whether to containers or even the next generation of technology. Places to start are:
- Eliminate hard dependencies through patterns like feature flags and permitting backwards compatibility for service calls (service versioning). You shouldn't care if another application you depend on has a release and they shouldn't care if you have a release. Ditto for database changes as well.
- Use object-based storage options or externalize your database from the PaaS-Container platform entirely. The fact is that your app will move across virtual hardware in ways that you can't control. Simplify the problem and leverage existing assets where you can.
- Rely on layer 7 security rather than network-based access controls for the services that you depend on. Due to multiple applications co-existing on PaaS Containers and the reliance on legacy services that won't exist on that platform, tried-and-true network controls for access to assets are insufficient. Change the model so your application has access to what it needs.
We recognize that everything can't change at once and it will take time to figure out where all of the enterprise applications fit in this context. But, by employing the thought processes and approaches above, we've found simple ways to embrace innovation in a secure enterprise context without waiting, over engineering, or even changing organization structure.
Slightly adjusting how we think about the advantages that new technology offers is enabling us to make applications more resilient, more adaptable, and more innovative to drive the business regardless of the underlying technology. Period.
#guerrilla_ea