Tom Jackman's contributions

Article
Android SPKI Pinning with TrustKit
Tom Jackman
Introduction In this blog post, I will demonstrate how to perform SPKI (Subject Public Key Info) Pinning in an Android Application using TrustKit - a pinning library for Android. Pinning Approaches One of the most common approaches for pinning in a mobile app is to store the certificate in storage. However, when server certificates are rotated, a new update to the application would likely need to be pushed out since the certificate in the application is no longer valid, possibly...
Article
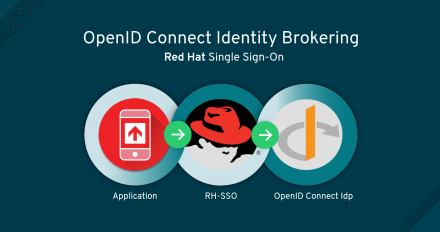
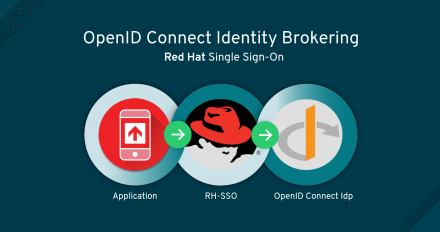
OpenID Connect Identity Brokering with Red Hat Single Sign-On
Tom Jackman
Introduction In this post, I will provide a walk through of how to set up Identity Brokering on an RH-SSO server. Red Hat Single Sign-On (RH-SSO) provides Web single sign-on and identity federation based on SAML 2.0, OpenID Connect and OAuth 2.0 specifications. For this tutorial, you will need: An RH-SSO Instance. A Web/Mobile Application with an OpenID Connect adapter. An OpenID Connect Provider Server (Such as Keycloak) to be used as the 3rd Party Identity Provider. Identity Brokering To...

Article
The Diamond in the Rough: Effective Vulnerability Management with OWASP DefectDojo
Tom Jackman
Managing the security of your projects applications can be an overwhelming and unmanageable task. In today's world, the number of newly created frameworks and languages is continuing to increase and they each have their own security drawbacks associated with them. The wide variety of security scanners available can help find vulnerabilities in your projects, but some scanners only work with certain languages and they each have different reporting output formats. Creating reports for customers or managers and viewing analytics using...
Article
Using Snyk, NSP and Retire.JS to Identify and Fix Vulnerable Dependencies in your Node.js Applications
Tom Jackman
Introduction Dependency management isn’t anything new, however, it has become more of an issue in recent times due to the popularity of frameworks and languages, which have large numbers of 3rd party plugins and modules. With Node.js, keeping dependencies secure is an ongoing and time-consuming task because the majority of Node.js projects rely on publicly available modules or libraries to add functionality. Instead of developers writing code, they end up adding a large number of libraries to their applications. The...

Article
Android SPKI Pinning with TrustKit
Tom Jackman
Introduction In this blog post, I will demonstrate how to perform SPKI (Subject Public Key Info) Pinning in an Android Application using TrustKit - a pinning library for Android. Pinning Approaches One of the most common approaches for pinning in a mobile app is to store the certificate in storage. However, when server certificates are rotated, a new update to the application would likely need to be pushed out since the certificate in the application is no longer valid, possibly...
Article
OpenID Connect Identity Brokering with Red Hat Single Sign-On
Tom Jackman
Introduction In this post, I will provide a walk through of how to set up Identity Brokering on an RH-SSO server. Red Hat Single Sign-On (RH-SSO) provides Web single sign-on and identity federation based on SAML 2.0, OpenID Connect and OAuth 2.0 specifications. For this tutorial, you will need: An RH-SSO Instance. A Web/Mobile Application with an OpenID Connect adapter. An OpenID Connect Provider Server (Such as Keycloak) to be used as the 3rd Party Identity Provider. Identity Brokering To...

Article
The Diamond in the Rough: Effective Vulnerability Management with OWASP DefectDojo
Tom Jackman
Managing the security of your projects applications can be an overwhelming and unmanageable task. In today's world, the number of newly created frameworks and languages is continuing to increase and they each have their own security drawbacks associated with them. The wide variety of security scanners available can help find vulnerabilities in your projects, but some scanners only work with certain languages and they each have different reporting output formats. Creating reports for customers or managers and viewing analytics using...
Article
Using Snyk, NSP and Retire.JS to Identify and Fix Vulnerable Dependencies in your Node.js Applications
Tom Jackman
Introduction Dependency management isn’t anything new, however, it has become more of an issue in recent times due to the popularity of frameworks and languages, which have large numbers of 3rd party plugins and modules. With Node.js, keeping dependencies secure is an ongoing and time-consuming task because the majority of Node.js projects rely on publicly available modules or libraries to add functionality. Instead of developers writing code, they end up adding a large number of libraries to their applications. The...
