
Using Let's Encrypt with Apache httpd on Red Hat Enterprise Linux 7
We show how to simplify SSL certificates using Let's Encrypt with Apache httpd on Red Hat Enterprise Linux 7.

We show how to simplify SSL certificates using Let's Encrypt with Apache httpd on Red Hat Enterprise Linux 7.
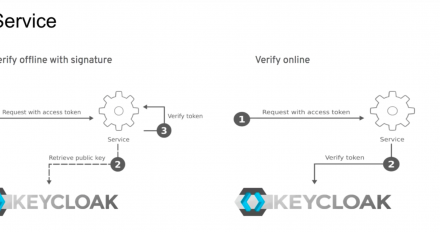
Learn how Keycloak can help you secure your microservices in this video demonstration from Sebastien Blanc.

Instructions in the NOP space are an attractive way to provide new performance and security features; we show how to use them effectively.
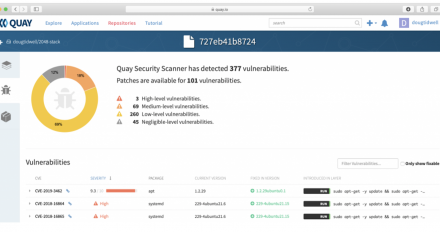
Quay.io is a container image repository that automatically scans your images for security vulnerabilities. Learn how to use this powerful feature.

We share some recent improvements for go-toolset, including a feature that lets Go call into a FIPS 140-2 validated cryptographic library.

A DevNation Live session - Easily secure your cloud-native microservices with Keycloak

In this article, we'll show how you can access Linux services remotely from .NET using SSH port forwarding.

The key steps for installing Red Hat Enterprise Linux 8 as a VirtualBox VM to get you started with software development.

This article covers how the -fstack-check capability in GCC works and explains why it is insufficient for mitigating Stack Clash attacks.

This article talks about multiple layers of security available while deploying Red Hat Data Grid on OpenShift. The layers of security offer a combination of security measures provided by Data Grid as well as by OpenShift/Kubernetes.
This article shows how to use the libFuzzer library with your applications so you can test how your applications handle arbitrary inputs from users.
This article describes how Red Hat Single Sign-On uses open source technology to provide a true multi-site single sign-on authentication platform capable of handling next-generation applications.
This article describes how to download and install Red Hat Single Sign-On for no cost. Red Hat Single Sign-On is an easy-to-use access management tool that takes care of the details of most authentication protocols, user consent with UMA, and even access control.
How to get a valid public certificate for your Red Hat Single Sign-On instance using Let's Encrypt and Lego. This avoids the inherent problems with self-signed certificates.

Annocheck a new utility to examine how a binary was built and to check that it has all of the appropriate security hardening features enabled. It also has several other modes that perform different kinds of examination of binary files.

Improve your application's security and close vulnerabilities with improved
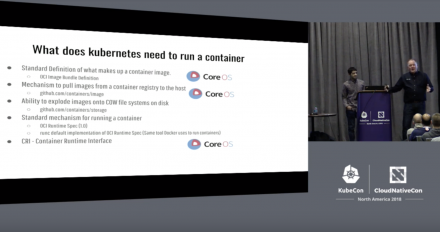
Video: Security Considerations for Container Runtimes. Explains/demonstrates using Kubernetes with different security features for your container environment.

Develop applications on the most popular Linux for the enterprise.
For times when you can't use ssh-copy-id to add your public key to a server, this article explains how to do it manually and set the correct permissions.

This post describes how to secure ASP.NET Core applications on OpenShift using HTTPS for two use-cases: terminating SSL in OpenShift for public routes and terminating SSL in ASP.NET Core directly using OpenShift-generated service certificates.

Learn how to secure your APIs using OIDC authentication via an external Identity Provider such as the IdPs from Microsoft and Oracle with Red Hat 3scale API Management.

Learn how to configure NGINX to use Keycloak/Red Hat SSO for authentication with OAuth/OIDC for federated identity. In this setup, Keycloak will act as an authorization server in OAuth-based SSO and NGINX will be the relaying party.
This post shows how to set up LDAP authentication on Red Hat AMQ 7. As part of the procees, it describes how to configure AMQ to authenticate users from LDAP and allow only users from a specified group to access the AMQ management console and publish messages in queues.

This session will give you a great introduction to Keycloak, an open source identity and access management solution for modern applications and services.

Watch this DevNation Live video to learn how to secure apps and services with Keycloak. Examples shown cover REST with Node.js, PHP, and HTML5.