Red Hat Developer Program introduces new topic on secure programming


(Part 2)Learn about recommended practices for producing secure code with input validation in part one of this four-part video series.

Learn how to start adopting a security-like mentality, also known as the "security mindset" in part four of this four-part video series.

Learn how to start adopting a security-like mentality, also known as the "security mindset" in the first half of part four in this four-part video series.

Learn about authorization such as user privileges, levels of access, and how they're different in part three of this four-part video series.

Learn about numeric errors and the dangers of using incorrect data types in part two of this four-part video series.

(Part 1)Learn about recommended practices for producing secure code with input validation in part one of this four-part video series.





Related Blog Post : https://developers.redhat.com/blog/2017/05/25/easily-secure-your-spring-boot-applications-with-keycloak/ Support Github repo : https://github.com/sebastienblanc/spring-boot-keycloak-tutoria Although security and identity management is a crucial aspect for any application, its implementation can be difficult. Worse, it is often neglected, poorly implemented and intrusive in the code. But lately, Identity Management servers has appeared which allow to outsource and delegate all authentication and authorization aspects. Of these servers, one of the most promising is Keycloak, open-source, flexible and agnostic of any technology, it is easily deployable / adaptable in its own infrastructure. In this session, I propose you to discover KeyCloak progressively and in an interactive way: 0 slide, 100% live coding."

Although security and identity management is a crucial aspect of any application, its implementation can be difficult. Worse, it is often neglected, poorly implemented and intrusive in the code. But lately, Identity Management servers has appeared which allow to outsource and delegate all authentication and authorization aspects. Of these servers, one of the most promising is Keycloak, open-source, flexible and agnostic of any technology, it is easily deployable / adaptable in its own infrastructure. In this session, I propose you to discover KeyCloak progressively and in an interactive way: 0 slide, 100% live coding."
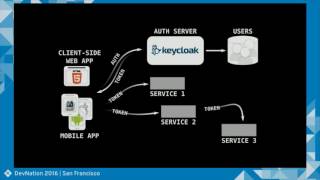
Learn how to use a centralized authentication service to secure many different microservices.

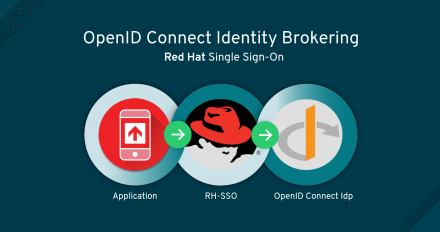
Corinne takes us through Swift development with AeroGear and how to use the new OAuth2 library to authenticate against Google Services. She also shows how to use Keycloak to secure REST endpoints and access them via AeroGear.

Keycloak is a new open source authentication server for cloud, mobile and html5. With loads of features, including single-sign on, social login, account management console, account workflows, fully featured admin console, OAuth2 and OpenShift cartridge to name a few. The first alpha has recently been released, with loads more features planned for the future. Keycloak also provides support for role based authorization and supports granting access to third party applications. This talk gives a comprehensive introduction to Keycloak and its features, as well as discuss how easily you can add authentication to your applications. There will also be an extensive live demo. Stian Thorgersen is a Senior Software Engineer at Red Hat. He co-leads the Keycloak project together with Bill Burke, and is also the security lead on another new open source project. Stian also has many years of experience in cloud solutions.