
iptables: The two variants and their relationship with nftables
Explore the relationship between iptables and nftables, and discover how iptables-nft gives you the best of both worlds without breaking legacy code.

Explore the relationship between iptables and nftables, and discover how iptables-nft gives you the best of both worlds without breaking legacy code.

Compare Kubernetes development to OpenShift's CLI and native extension API resources, including build configs, deployment configs, and image streams.
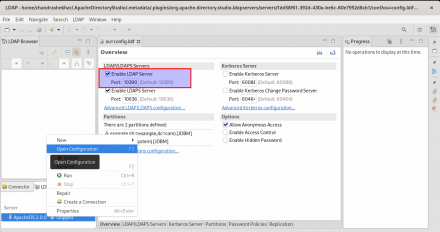
Learn how to integrate Red Hat AMQ 7.7 with Apache Directory Studio, which is an LDAP browser and directory client for ApacheDS.
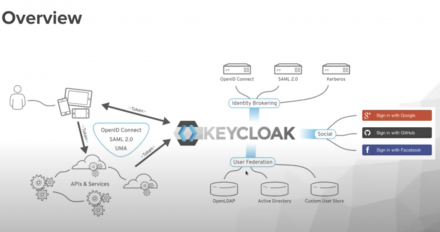
In this DevNation Tech Talk, we take a deep dive into Keycloak to handle open source identity and access management with modern applications and services.
Learn the basics of SELinux, including type enforcement, Multi-Category Security (MCS) Enforcement, and Multi-Level Security (MLS) Enforcement, with the help of some friendly cats and dogs!
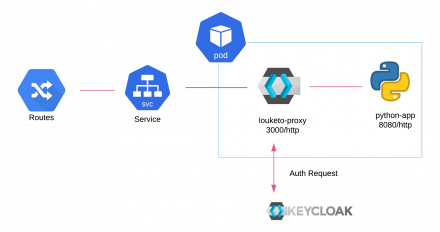
Learn how to use Louketo Proxy as a sidecar to provide authentication for your microservices that are built using multiple languages.

Secure Vue.js apps with Keycloak | DevNation Tech Talk

Discover the new features in Open Liberty 20.0.0.7, which give you more control over JWT cookies for SSO, LTPA cookies for TAI or SPNEGO, and more.
Secure your Quarkus applications | DevNation Tech Talk

Securing distributed software systems might seem more complex than ever, but the working principles of good software security haven't really changed.

Security and authentication strategies for apps on Kubernetes | DevNation Tech Talk

Keeping Kubernetes secrets secret | DevNation Tech Talk
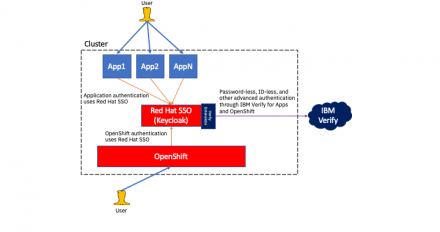
Learn how IBM Security Verify provides advanced authentication to Red Hat SSO environments while also balancing id-less and password-less experiences.
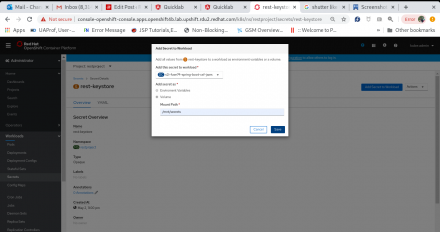
Configure a keystore for a Java-based web service or HTTP endpoint, and a truststore for a web service client, HTTP client, or messaging client.

Discover the design principles and performance improvements behind GCC's code generation strategies for defending against stack clash attacks.
Discover the new -fanalyzer option coming to GCC 10 that provides a static analysis pass to identify problems at compile-time, rather than at runtime.
JSON Web Tokens (JWT) are a web standard–RFC 7519–but using them with Eclipse MicroProfile may be a mystery. This cheat sheet by Red Hat Senior Software Engineer Martin Stefanko will help you get moving immediately.
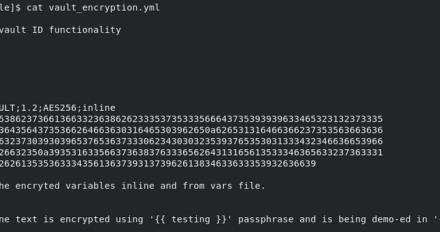
Learn how to enable the use of multiple Ansible vault passwords through vault IDs to encrypt a file and a string.
Learn how to generate a JWT token and then validate it using API calls, so Keycloak's UI is not exposed to the public.

Find out how NGINX can act as a reverse proxy server for back-end applications, which can be hosted on an enterprise application server.
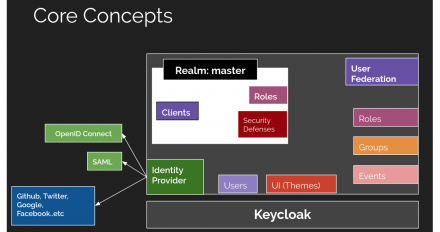
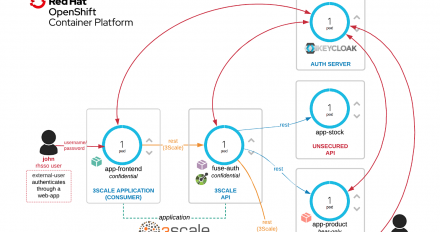
We show a practical example on how to secure modern applications and microservices with Red Hat Single Sign-On, Fuse and 3scale.

How to sign and verify signatures of container images using podman and skopeo

The basic steps of container security involve securing the build environment, securing the container hosts, and securing the content running inside.

See how the keycloak-saml adapter can be configured in the place of Picketlink to enable SAML-based authentication with a third-party identity provider.