
Every layer counts: Defense in depth for AI agents with Red Hat AI
Learn how Red Hat AI can help address the security challenges of AI agents in production, from semantic malware to container escapes.

Learn how Red Hat AI can help address the security challenges of AI agents in production, from semantic malware to container escapes.

Learn about some of the quirks of running a build command in a distroless image.

Scale agentic AI with Red Hat’s trusted software factory. Use Policy as Code and SBOMs to strengthen your development pipeline and manage software provenance.
Deploy confidential containers and CVMs for AI. Learn how the Red Hat build of Trustee automates attestation to protect patient data on OpenShift and RHEL.

Learn about Red Hat Hardened Images, small containers that incorporate a minimal set of files for delivering purpose-built applications.

Learn how to federate identities in an OpenShift environment to enable access to multiple cloud storage providers without the use of static credentials.
This article re-evaluates dm-crypt/LUKS storage protection against host-based attacks, detailing threats like key theft and unsafe volume unlocking.

Learn how to use Project Hummingbird and Calunga open source projects to build application containers with Red Hat Hardened Images and trusted libraries.

Learn about our team's experience implementing a defense-in-depth safety architecture for AI agents using Llama Stack shields.

Explore the benefits and use cases of Project Hummingbird, a collection of minimal, hardened, distroless container images.
Learn how to integrate a Linux virtual machine with Red Hat OpenShift Service
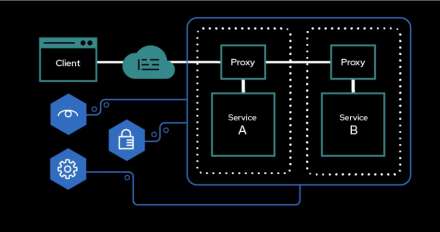
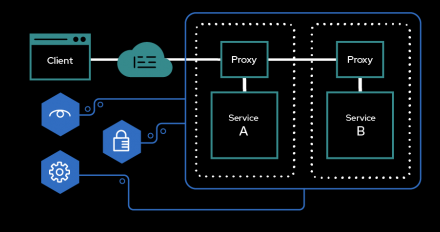
Explore how Red Hat OpenShift Service Mesh, Red Hat OpenShift Service Mesh, and

Learn how to execute Red Hat Ansible Automation Platform automations in a hybrid environment using a cloud-hosted management cluster controlling on-premise bare-metal Red Hat OpenShift Virtualization clusters. This approach eliminates the need for dedicated execution nodes, leverages cloud-native capabilities, and reduces latency.

Explore how Red Hat AI simplifies agent deployment with OpenClaw, showcasing model inference, safety guardrails, agent identity, and persistent state. Learn about vLLM, Llama Stack, and Models-as-a-Service (MaaS) options, and discover the benefits of agent identity and zero trust with Kagenti and AuthBridge.

How to implement TAPaaS for scalable, on-demand traffic mirroring in Red Hat OpenStack Services on OpenShift, which is essential for security and observability.

Learn how Fromager, an open source project, helps protect Python dependencies by rebuilding entire dependency trees from source, providing network-isolated builds, and managing dependencies as a verifiable map. Discover how Fromager ensures supply chain verifiability, ABI compatibility, and customization.

Learn how to enable Firewall-as-a-Service (FWaaS) in OpenStack Services on OpenShift to enhance security in multi-tenant, OpenStack-based clouds.
Discover improved network observability: the DNSTracking feature now reports DNS query names, DNS latencies, and response codes for Kubernetes cluster resolutions.

Learn how Keylime's new push model addresses the issues of attack surface, network complexity, scaling, and rigidity in traditional remote attestation methods. Discover the benefits of the push model in Red Hat Enterprise Linux 10.2 and its availability in the Rust agent and Python verifier.
Discover how OpenShift Commatrix CLI solves firewall misconfiguration in OpenShift by automatically generating ingress communication matrix for your specific cluster. Learn about key improvements over manual approach.
Learn how to reproduce Hummingbird images using cosign and podman. This process ensures software supply chain security by verifying the image's bit-for-bit identity. Discover the steps to rebuild a Hummingbird image and maintain reproducibility.

Learn how to set up and run a local AI audio transcription using an Red Hat open source model.
Discover a solution for simplifying and automating the management of multi-network policies (MNP) at scale using Red Hat Advanced Cluster Management.

Learn how to manage the security threats and access controls associated with adopting the new Agent Skills functionality.
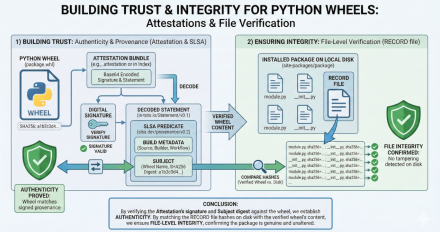
In this blog post, we're looking at how the Tech Preview of Red Hat Trusted