
4 steps to set up 3scale access tokens
Learn how to set up single-use access tokens in Red Hat 3scale API Management to enhance application security with this X-step demo.

Learn how to set up single-use access tokens in Red Hat 3scale API Management to enhance application security with this X-step demo.
Follow the instructions in this article to quickly connect a Red Hat single sign-on technology client with a Red Hat Data Grid server on Red Hat OpenShift.

The GNU C Library's 2.33 release adds buffer overflow protection for C/C++ programs. Find out how _FORTIFY_SOURCE=3 improves overflow protection in glibc.

Get started with using Red Hat CodeReady Dependency Analytics to analyze dependency vulnerabilities in your Golang application stack.

Set up authentication and authorization to connect Red Hat Integration Service Registry with a secure Red Hat AMQ Streams Kafka cluster.

Get a quick introduction to C and C++ code analysis with clang-tidy, including checking for rule violations and integrating clang-tidy with a build system.

Improving security with Istio | DevNation Tech Talk
Discover what's new in Red Hat JBoss Enterprise Application Platform 7.4 beta, including new security, server management, and developer features.

Configure a browser authentication flow using X.509 user-signed certificates with Red Hat's single sign-on technology and OpenSSL.
Red Hat Developer Program Terms and Conditions
Get an overview of fixes and enhancements to the -fanalyzer static analysis pass, currently being updated for security, state tracking, and more in GCC 11.
How to enable HTTPS and SSL Termination in an already running Quarkus application in Openshift.

Learn how to restrict or limit access to applications that are federated with Keycloak for users authenticating through a third-party provider.
Learn how to integrate Red Hat's single sign-on tools version 7.4 with Red Hat Directory Server 11 (LDAP), and synchronize users and groups between the two.
Discover connection pooling, and then learn how to use Oracle's Universal Connection Pool with an Oracle RAC database in a JBoss EAP deployment.

Learn how to go beyond the simple login API and enable the full force of Keycloak's authentication and authorization features using the Keycloak REST API.
Set up Multus-CNI and CDI DataVolumes in KubeVirt to configure your network and storage requirements for high performance, security, and scalability.
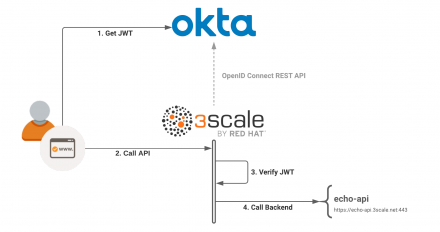
Set up a 3scale and OpenID Connect integration and authorization flow using Okta as your OIDC provider and JSON Web Token and Oauth2 for verification.
Explore the Red Hat 3scale API Management 2.9 highlights, including air-gapped installation on Red Hat OpenShift and new APIcast policies.

Protect your Red Hat OpenShift secrets. Learn how to use PKCS #11 URIs and libssh to store private information in highly secure hardware tokens.

Use Keycloak's authentication service provider interface to develop a custom MobileAuthenticator class that you can run in your JBoss EAP container.
Learn how to configure a Quarkus application with Red Hat Data Grid and deploy it on Red Hat OpenShift with Data Grid 8.1's new security features.

Explore the new Automatic Certificate Management Environment (ACME) protocol support available through the Open Liberty 20.0.0.10 Java Red Hat Runtime.
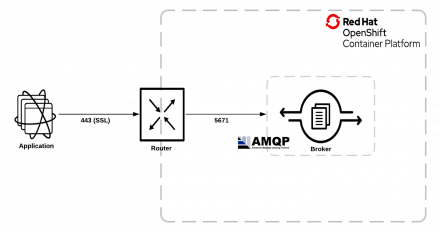
Learn how to connect external clients to Red Hat AMQ Broker using the SSL or TLS protocol when deploying on Red Hat OpenShift.
Red Hat CodeReady Workspaces 2.3 brings two ways to inject secrets, cluster-wide proxy support, devfile and IDE plugin updates, and more.