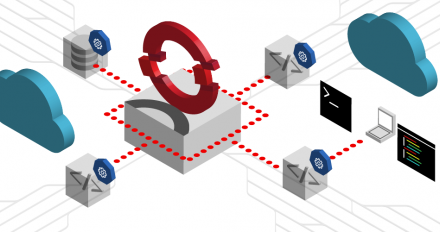
Implement a cross-cloud identity framework with SPIFFE/Spire on OpenShift
Address cross-cloud identity challenges with SPIFFE/SPIRE on Red Hat OpenShift
Address cross-cloud identity challenges with SPIFFE/SPIRE on Red Hat OpenShift
"Kubernetes Secrets Handbook" is a treasure for developers, users, laymen and
Learn how workstation users authenticating to Active Directory using the Kerberos protocol can use SPNEGO tokens with Red Hat build of Keycloak.

Learn how to set up Red Hat build of Keycloak as an Identity Broker on OpenShift using Active Directory Federation Services as a SAML 2.0 Identity Provider.

Introducing a new video series staring Red Hat's Dan Walsh, with technical deep
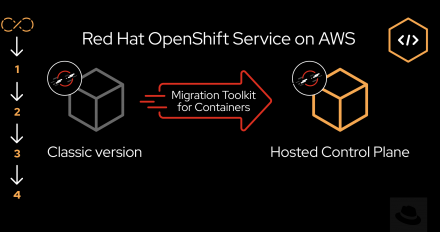
Explore how the migration toolkit for containers (MTC) paves the way for

This article guides you through migrating from Red Hat single sign-on to Red Hat build of Keycloak, a next-generation identity and access management solution.
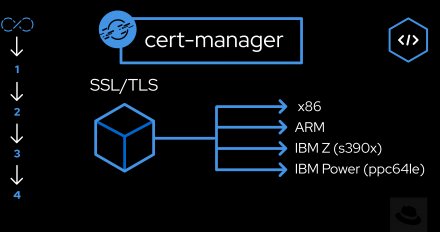
Learn efficient certificate management techniques on Red Hat OpenShift using the
Download this e-book to learn key concepts for building security into your software supply chain, along with best practices for implementation.

A common platform for machine learning and app development on the hybrid cloud.

Applications based on machine learning and deep learning, using structured and unstructured data as the fuel to drive these applications.

Red Hat Trusted Software Supply Chain is a family of products aiming at exactly that:providing security for the software supply chain from coding to execution monitoring.
Learn why crucial software supply chain security maturity is crucial for modern developers to ensure they are building and deploying secure software.

Discover how Red Hat Trusted Software Supply Chain makes it easier to create, deploy, and host security-focused applications in the container era.

Explore a highly available (or fault tolerant) Keycloak solution that you can manage through multiple single instances of Keycloak, all using the same user directory source.
The Red Hat OpenShift application platform is comprised of many components

Learn how to secure a simple JBoss EAP 8.0 web application with Microsoft Azure authentication via OpenID Connect in this tutorial.

Learn how to install the Red Hat Trusted Artifact Signer using Google identity

Red Hat Trusted Profile Analyzer lets you track software components across the build and deployment of your applications.
Learn best practices for adding or improving the support of your component for Red Hat Enterprise Linux in FIPS mode.
Get an overview of key security best practices for Red Hat OpenShift Dev Spaces that can help foster a more resilient development environment.

Learn how to getting started with Red Hat build of Keycloak in this short demo.

Get an introduction to SCAPinoculars, a tool that helps you to visualize OpenSCAP reports, and the advantages it brings when used with the OpenShift Compliance Operator.

Explore the motivation behind the GNU toolchain project's new security policies and why more open source communities should adopt policies for their projects.

Learn how to use the Prometheus monitoring tool to scrape metrics from Red Hat build of Keycloak deployed on OpenShift.