You've created a container image that has all the packages that you and your team need to do something useful, or maybe you've built a public image that anybody can use. But, what if that image contains packages with known security vulnerabilities? Regardless of the severity of those vulnerabilities, you'll want to learn more and take steps to mitigate them as soon as possible.
Fortunately, your team uses Quay.io* as your registry. When you push an image to Quay.io, it automatically runs a security scan against that image.
Here are the results of the latest scan for an image I built a few months ago for an article about creating custom stacks for Eclipse Che:
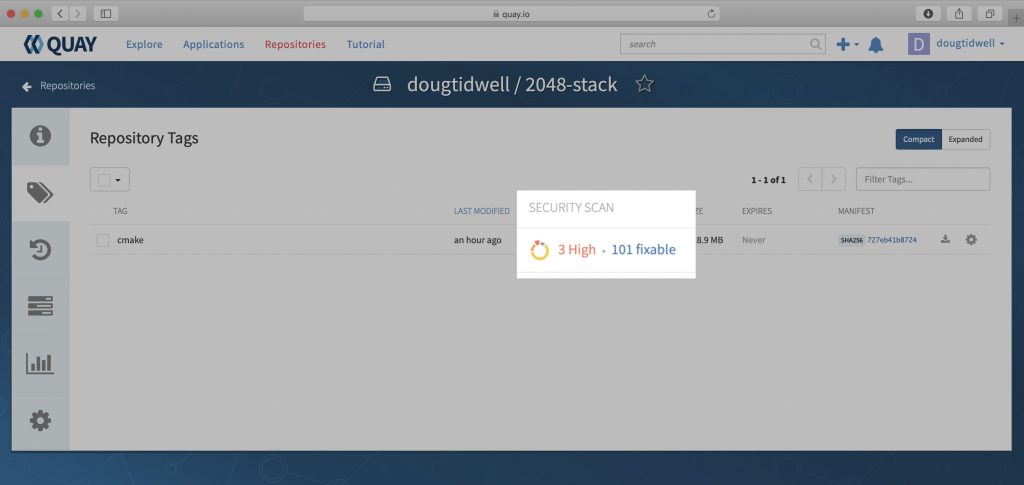
As you can see, I found to my dismay that there are three security vulnerabilities ranked High. They weren't there when I built the image; they've been discovered since I pushed the image to the registry. Hopefully, they're included in the 101 vulnerabilities labeled Fixable. Clicking on 101 fixable gives a list of all the vulnerabilities and their fixes—if any—as shown in the following screenshot.
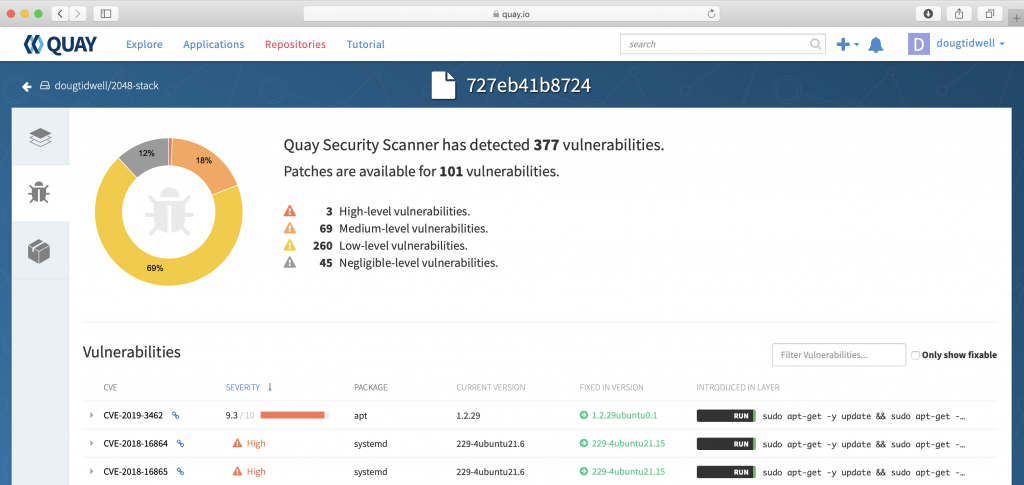
Fortunately, all three of the high vulnerabilities have fixes. In this image, the leftmost column lists the CVE number for each vulnerability. (CVE stands for Common Vulnerabilities and Exposures, a reference method for publicly known issues.) Clicking the link icon next to the CVE number takes you to the actual vulnerability report. Together, these resources will give you all the available information about the issues identified by the security scan.
Again, the three high vulnerabilities all have fixes, as shown in the Fixed in version column. If we rebuild the image and push it back to Quay.io, it will automatically be rescanned. If we're lucky, all of the fixes will be applied, and our new image will be safe for the world once more.
We can improve our luck by making sure any updates and upgrades are applied to the new image. My Dockerfile starts like this:
# Base the image on the standard C++ stack
FROM eclipse/cpp_gcc
# Basic system hygiene
RUN sudo apt-get -y update && \
sudo apt-get -y upgrade && \
The update and upgrade commands for your distribution manager (apt-get, yum, dnf, etc.) ensure that all of the packages in the base image are updated and upgraded before the image build continues.
Pro tip: Using the Linux AND operator (&&) lets you execute multiple commands with a single RUN statement. That prevents your image building tool (podman or docker) from creating a separate layer for each command.
After I rebuilt the image and pushed it back to Quay.io, the security scan looks much better:
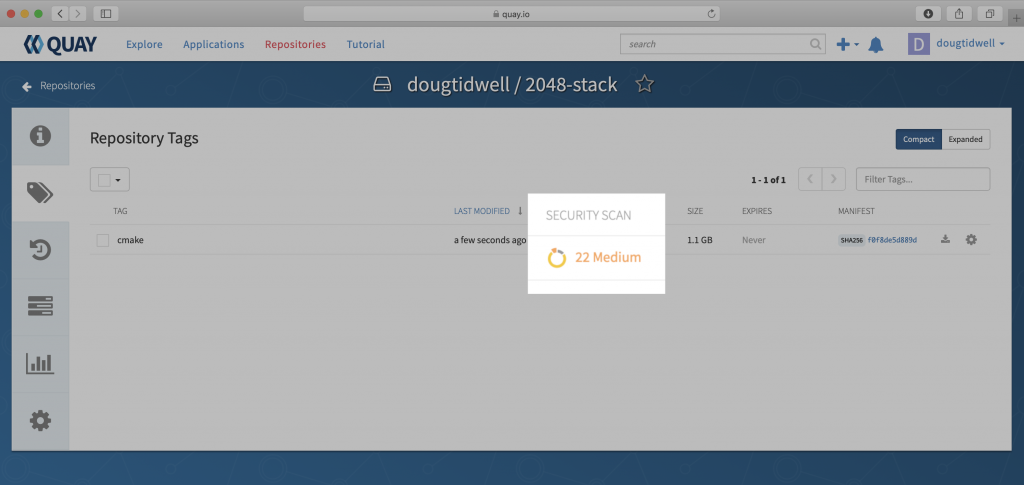
We don't have any high vulnerabilities now. Opening the report and clicking the Only show fixable checkbox shows that the package repositories we're using do not have any fixes yet for the problems Quay.io found:
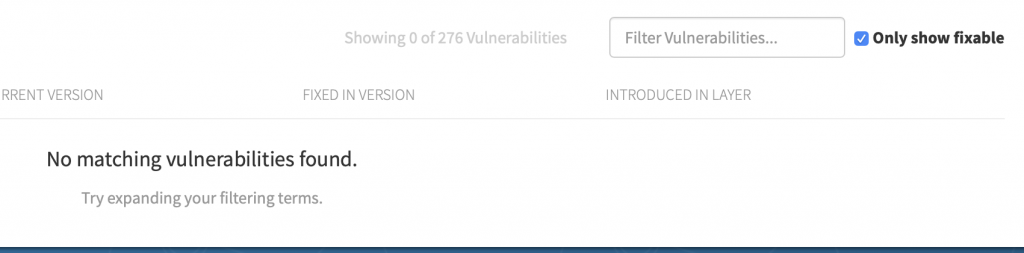
Now it's time for a judgment call. Unchecking "Only show fixable" displays the entire list. You can then look at the CVE report for each item and decide whether it's crucial to fix any of your remaining vulnerabilities. If so, you may be able to find a fix outside the package repositories you're using. (There is usually a lag of a few days between the time a fix is released and the time it shows up in the repos.) If a fix exists elsewhere, you'll have to do something like updating your Dockerfile to use curl to get the fix and then using your platform's install tool to add it to your image.
Quay.io scans your image periodically, so it's a good idea to check your image on a regular basis. When you do, you'll see an up-to-date list of any vulnerabilities in your image along with the information you need to evaluate them. Red Hat Quay is also available as a separate product so you can create private registries that deliver the same features.
With Quay.io's security scans, you can make sure your image is as safe and secure as possible.
* Although the English-speaking world outside of the United States pronounces this word "key," the product is officially pronounced "kway." (Google Translate pronounces it "key" as well.) I'm just the messenger here.
Last updated: February 11, 2024