As you would expect, security is a key focus for Red Hat. Secure by default is more than a goal, it is a guiding principle across all product lines. Middleware is no exception and there are some amazing things going on in this space. Divya Mehra and Vikas Kumar of Red Hat walked us through some of the recent innovations, including the recently released Red Hat SSO, product built upon KeyCloak. Derek Walker of SWIFT also spoke about how the leading financial system message broker relies upon JBoss Fuse for secure messaging.
Security is one of the most important topics in computing today, it can be separated into three key pillars and further mapped into middleware features:
- Confidentiality
- Authentication
- Authorization
- Integrity
- Audit logging
- non-repudiation
- Availability
- Clustering
- Guaranteed Delivery
In short, Red Hat JBoss Middleware is secure and open source throughout the entire product line, giving customers increased assurances, such as:
- Known, fully open source components
- built securely from source
- Proactive security notifications and fixes
- Standards-based
- OpenJDK
- SAML 2.0, Kerberos, OpenID Connect
- TLS, WS-security
Red Hat SSO is the newest member of this product line, providing a brand new server for complete identity management federation:
- SAML 2.0
- OpenID Connect
- OAuth 2.0
It also comes with client adapters, allowing customers to easily integrate their applications with Red Hat SSO or other standard-compliant identity provider.
Red Hat SSO server is a complete, stand-alone product and is Red Hat's solution for web-based federation. It can interface with Red Hat Identity Management (IdM) for integration with internal corporate identity management. It can also work with Active Directory and plain LDAP. There is native OpenStack and OpenShift integration with Red Hat SSO coming down the line as well.
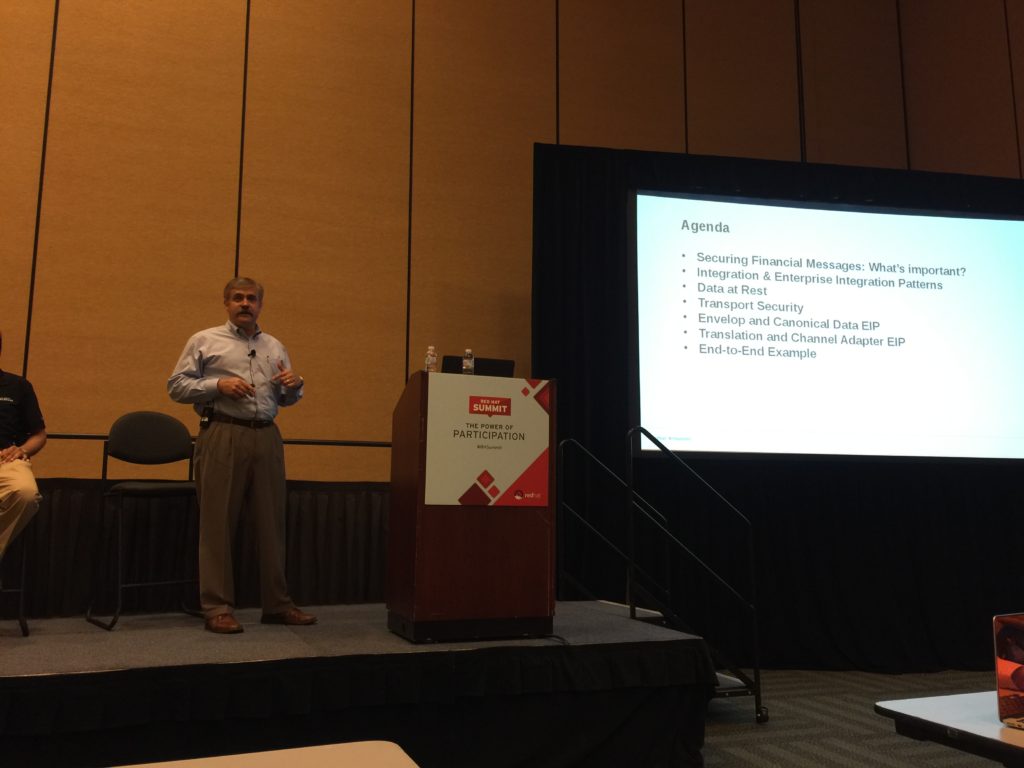
Case Study - SWIFT (JBoss Fuse)
The SWIFT system is widely used for financial transactions across the globe. Derek walked us through some security basics and patterns when developing secure integration on JBoss Fuse.
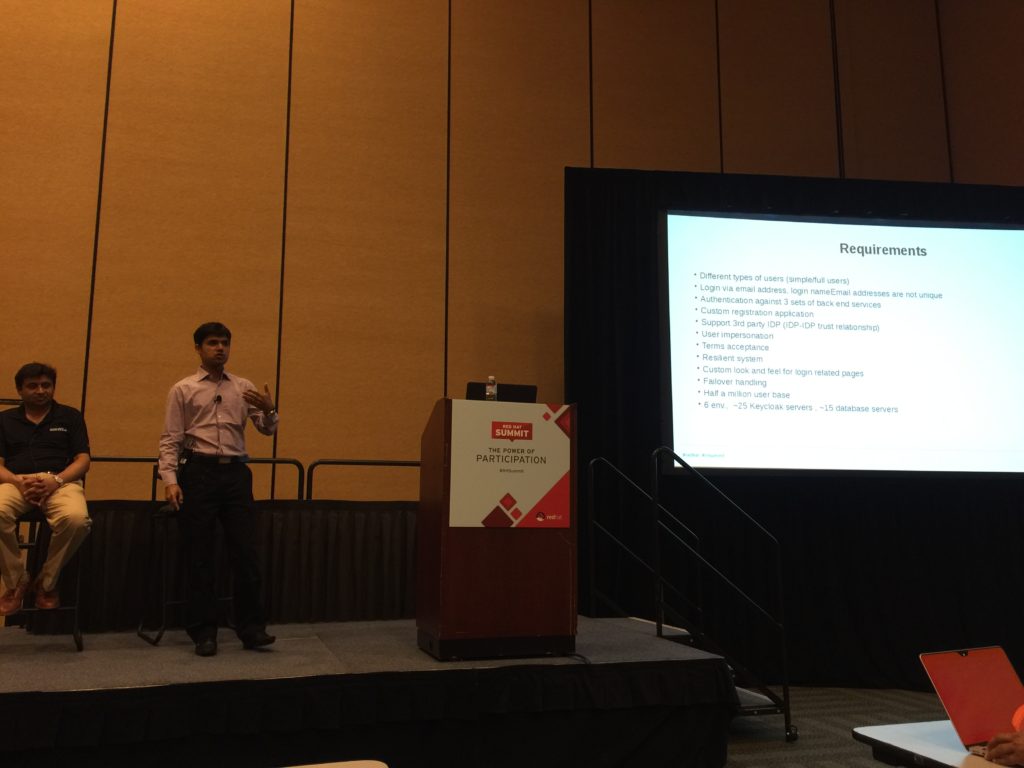
Case Study - Red Hat SSO deployed in production
Red Hat IT recently deployed Red Hat SSO as the SAML Identity Provider for http://www.redhat.com and http://access.redhat.com. If you have logged into the Customer Portal recently, you consumed this new technology. The multi-region, highly available deployment was just the beginning. Thanks to the broad set of features supported by Red Hat SSO, Red Hat IT is now in a position to take advantage of technologies including two factor authentication, SAML 2.0, social authentication, OAuth 2.0 and OpenID Connect.
About the Author
Brian J. Atkisson is a Senior Principal Systems Engineer and the technical lead on the Red Hat IT Identity and Access Management team. He has 18 years of experience as a Systems Administrator and Systems Engineer, focusing on identity management, virtualization, systems integration, and automation solutions. He is a Red Hat Certified Architect and Engineer, in addition to his academic background in Biochemistry, Microbiology and Philosophy.
Last updated: March 15, 2023